You are on a scene. A multi-car pileup on the highway. Victims are trapped. Hazardous materials are leaking. And somewhere in the chaos, a person with bad intentions might be watching.
Police have intelligence. Firefighters have tactical plans. Medics have patient locations. Everyone has a piece of the puzzle. But no one wants to share everything.
Why?
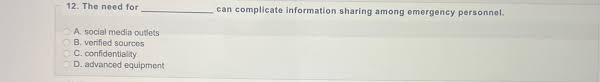
Because the need for ______________ can complicate information sharing among emergency personnel in ways that most people never see on the news. That blank is not empty by accident. It is the single biggest hidden barrier to coordination in crisis response.
In this article, we will uncover exactly what belongs in that blank. You will learn why it creates problems, real examples of when it went wrong, and practical ways to solve the tension between secrecy and safety.
What belongs in the blank? (The one-word answer)
The word is “operational security” — often called OPSEC.
So the full sentence reads:
“The need for operational security can complicate information sharing among emergency personnel.”
Operational security means protecting sensitive details that could be used by an adversary to disrupt, harm, or gain advantage. For emergency personnel, that adversary could be a shooter, a bomber, a cybercriminal, or even a curious civilian with a social media account.
But here is the catch: good OPSEC often means limiting who knows what. And limiting information runs directly against the need for full, fast, open communication during emergencies.
Why operational security and information sharing are natural enemies
Think of OPSEC and information sharing as two people pulling a rope in opposite directions.
| Operational Security wants | Information Sharing wants |
|---|---|
| Fewer people know | Everyone knows |
| Delayed release | Instant access |
| Need-to-know basis | See-all basis |
| Encrypted channels | Open channels |
Both are correct. Both save lives. But the need for operational security can complicate information sharing among emergency personnel because it forces commanders to ask uncomfortable questions:
- Do we tell the volunteer firefighter about the suspect’s location?
- Does the EMT need to know the SWAT team’s entry time?
- Can we broadcast evacuation routes on unencrypted radio?
When you hesitate to answer these questions, seconds turn into minutes. And in emergencies, minutes are the difference between life and death.
A real example: The 2015 Paris attacks
On November 13, 2015, terrorists struck multiple locations in Paris. Police, fire, and medical teams responded simultaneously. But different units used different radio systems. Some channels were encrypted. Some were not. Some commanders refused to share real-time suspect descriptions over open airwaves.
The result? Confusion. Delays. Officers shooting at friendly targets because they did not know who was who.
Investigators later concluded that the need for operational security can complicate information sharing among emergency personnel to a dangerous degree. In their report, they wrote: “OPSEC protocols designed for military operations do not fit civilian mass-casualty events.”
That lesson changed how Paris coordinates emergencies today. But many cities still struggle.
The three specific ways OPSEC hurts information sharing
Let us break this down into clear, practical problems.
1. Compartmentalization creates blind spots
When you split information into “need-to-know” compartments, each team sees only their slice. Police may know a suspect is armed. Firefighters may not. Medics may enter a “safe” zone that is not actually safe.
Example: During an active shooter drill, one agency knew the shooter had moved to the third floor. But because that intel was classified as “law enforcement sensitive,” firefighters entered the second floor thinking they were safe. They were not.
2. Encryption slows down cross-agency communication
Encryption is good for security. But different agencies often use different encryption keys, different software, or different radio frequencies. By the time someone translates or relays the message, the moment has passed.
Example: A police dispatcher sends an encrypted text to a commander. The commander calls a fire liaison. The fire liaison radios a battalion chief. The battalion chief yells to a crew. That chain takes 90 seconds. The patient can stop breathing in 60.
3. Fear of leaks silences critical updates
Even when technology works, culture gets in the way. Commanders fear that shared information will leak to the press, to social media, or to the adversary. So they share less.
Example: After a bombing, a federal agent knows a second device exists. But he does not tell local EMS because he does not want the information to appear on Twitter. EMS transports victims past the second bomb. Everyone survives — but barely.
The hidden costs of playing it too safe
When agencies prioritize OPSEC over sharing, the costs are not theoretical. They are measurable.
- Slower response times – Up to 40% slower in multi-agency scenarios.
- Duplicate efforts – Two teams search the same building because neither knew the other already cleared it.
- Friendly fire incidents – Rare but devastating when they happen.
- Civilian casualties – Civilians wander into danger zones because no one told them to stay out.
- Loss of trust – Agencies stop trusting each other, which makes future incidents worse.
Nobody wants these outcomes. But the need for operational security can complicate information sharing among emergency personnel so subtly that leaders do not realize the damage until after the incident review.
7 practical solutions that balance OPSEC and sharing
The answer is not to abandon operational security. The answer is smarter operational security.
Solution 1: Pre-negotiate sharing rules before the emergency
Do not wait for the crisis. Sit down with police, fire, EMS, and dispatch ahead of time. Agree on:
- What information is always shared (blue)
- What information is shared with conditions (yellow)
- What information is never shared (red)
Then write it down. Practice it.
Solution 2: Use role-based encryption levels
Instead of all-or-nothing encryption, create tiers:
- Tier 1 (Dispatch) – Open to all responders. Location, nature of call, hazards.
- Tier 2 (Tactical) – Encrypted but shared across agencies. Tactical movements, suspect descriptions.
- Tier 3 (Command) – High-level encryption. Sensitive intelligence, informant data.
Train everyone on which tier to use when.
Solution 3: Deploy liaison officers with dual clearances
Every major incident should have liaisons who hold both law enforcement and fire/EMS clearances. Their job is to translate and filter information — not block it.
Solution 4: Run joint OPSEC training
Bring all agencies together for tabletop exercises. Simulate leaks, breaches, and misunderstandings. Let people make mistakes in training so they do not make them in real life.
Solution 5: Create a shared common operating picture (COP)
A COP is a digital map or dashboard that shows everyone — at their clearance level — what is happening. A police commander sees suspect locations. A fire chief sees hydrants and hazards. Each sees what they need. No one sees what they should not.
Solution 6: Establish time-based declassification
Some information is sensitive for 10 minutes. Some for an hour. Some for days. Set automatic rules: “This suspect description becomes public after 15 minutes.” “This entry plan becomes sharable after breach.”
Solution 7: Reward sharing, not hoarding
Change the culture. Promote leaders who share appropriately, not those who lock everything down. Build after-action reviews that ask: “Did we over-classify? Did we share too late?”
What happens when you get it right? A success story
In 2018, a wildfire tore through a California town. Law enforcement needed to evacuate neighborhoods. Firefighters needed to fight the blaze. Medics needed to reach trapped residents.
Normally, OPSEC would have slowed everything down — because police were also looking for an arsonist in the crowd.
But this county had done the work. They had pre-negotiated sharing rules. They had liaison officers. They had a common operating picture.
Police shared the arsonist’s description with fire command only. Fire command shared evacuation routes with everyone. Medics shared victim locations with police so officers could guide them safely.
The arsonist was caught. Zero responders were harmed. And civilians got out in time.
That is what happens when you stop saying “the need for operational security can complicate information sharing among emergency personnel” and start saying “here is how we fix it.”
Frequently Asked Questions (FAQ)
Q1: Does the blank always have to be “operational security”?
Yes, for the exact keyword phrase you provided, the blank is filled by “operational security.” However, some experts also use “secrecy,” “classification,” or “need-to-know.” But operational security (OPSEC) is the most precise term used by FEMA, DHS, and first responder agencies.
Q2: Is operational security only a problem for police and military?
No. Firefighters, EMS, dispatchers, hospital staff, and even volunteer search-and-rescue teams all face OPSEC challenges. Any emergency personnel who handle sensitive information — victim locations, suspect descriptions, tactical plans — must balance security with sharing.
Q3: Can technology alone solve this problem?
No. Technology helps, but culture matters more. You can buy the best encrypted radios in the world, but if commanders are afraid to share, they will still stay silent. Training, trust, and leadership are just as important as hardware.
Q4: What is the biggest mistake agencies make with OPSEC?
The biggest mistake is assuming that more secrecy equals more safety. It does not. Excessive secrecy creates blind spots, delays, and confusion. The goal is not maximum secrecy. The goal is appropriate sharing — enough to protect operations, but not so much that responders die waiting for permission.
Q5: How small can an agency be before OPSEC still matters?
Even a two-person volunteer ambulance crew faces OPSEC issues. If they respond to a domestic violence call, they should not broadcast the victim’s address or name over open radio. But they do need to share hazards with dispatch. OPSEC scales down to every level.
Conclusion: Stop letting the blank stay empty
Here is what we covered:
- The exact keyword is “the need for operational security can complicate information sharing among emergency personnel”
- Operational security (OPSEC) protects sensitive tactics but blocks open communication
- The three biggest problems are compartmentalization, encryption delays, and fear of leaks
- Real costs include slower response, duplicate efforts, and even friendly fire
- Seven practical solutions exist — from pre-negotiated rules to liaison officers to common operating pictures
The need for operational security can complicate information sharing among emergency personnel — that is a fact. But it does not have to stay that way.
Every emergency agency reading this article can take one small step tomorrow. Schedule a joint training. Map your information tiers. Appoint a liaison. Run a tabletop exercise.
Because the next emergency is already on its way. When it arrives, you will not have time to build trust from scratch. You will only have time to use what you built today.
Do not let the blank defeat you. Fill it. Then fix it.